
Stop Your Smart Devices From Being Used To Spy On You
With so many smart devices now all around us in homes and offices,…
March 24, 2022/by jon hyde
3% of Users Responsible For 92% Of Breaches
A report by Security Company ‘Elevate’ has revealed that…
March 17, 2022/by jon hyde
Mobile Malware Surges By 500%
Proofpoint researchers have reported that, starting in early…
March 17, 2022/by jon hyde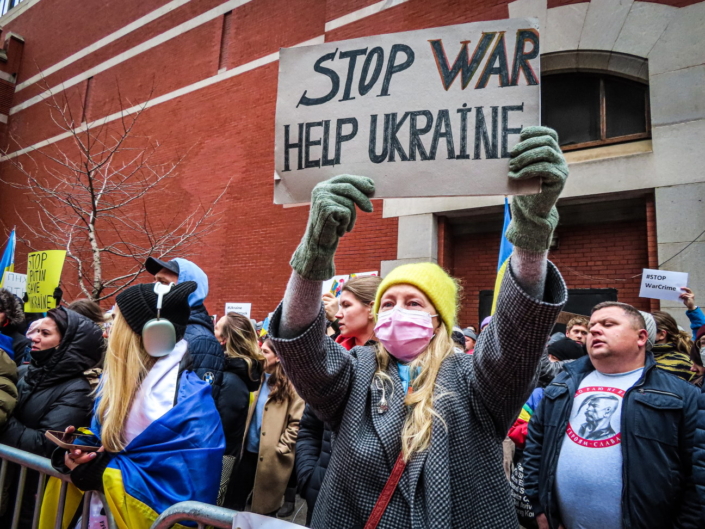
How Worried Should We Be About Cyber Warfare?
In this article we look at how cyber-attacks have been used…
March 3, 2022/by jon hyde
Ransomware Study : Most UK Firms Pay
A study by security firm ‘Proofpoint’ has revealed that…
March 3, 2022/by jon hyde
Firms Prepare For The Quantum Apocalypse
In this article, we look at what the ‘quantum apocalypse’…
February 25, 2022/by jon hyde
Why Solid Black Bars May Be Best For Redacted Text
In this insight, we look at how to best to avoid redacted text…
February 25, 2022/by jon hyde
Ex School IT Technician Jailed For Cyber Attack
A sacked school IT Technician who took revenge by deleting data…
February 25, 2022/by jon hyde
What Is The Online Safety Bill?
Following recent announcements of a toughening-up of the (draft)…
February 22, 2022/by jon hyde
How Microsoft Will Block Macros To Stop Malware
Microsoft recently announced that it will be blocking Visual…
February 22, 2022/by jon hyde
European Oil Facilities Targeted By Cyber Attacks
In a worrying trend, oil facilities in Germany, Belgium and…
February 10, 2022/by Stacey Hand
30% Rise In Crypto-Laundering
A report by blockchain data platform ‘Chainalysis’ has shown…
February 4, 2022/by jon hyde